« RustDesk » : différence entre les versions
Aller à la navigation
Aller à la recherche
| (4 versions intermédiaires par le même utilisateur non affichées) | |||
| Ligne 90 : | Ligne 90 : | ||
# mkdir -p /opt/rustdesk-api | # mkdir -p /opt/rustdesk-api | ||
# cd /opt/rustdesk-api | # cd /opt/rustdesk-api | ||
Fichier de configuration du conteneur : | |||
# vi docker-compose.yml | # vi docker-compose.yml | ||
| Ligne 113 : | Ligne 113 : | ||
RUSTDESK_API_RUSTDESK_RELAY_SERVER: "<font color = blue>monserveur.org</font>:2111" | RUSTDESK_API_RUSTDESK_RELAY_SERVER: "<font color = blue>monserveur.org</font>:2111" | ||
RUSTDESK_API_RUSTDESK_API_SERVER: "<nowiki>https</nowiki>://<font color = blue>monserveur.org</font>" | RUSTDESK_API_RUSTDESK_API_SERVER: "<nowiki>https</nowiki>://<font color = blue>monserveur.org</font>" | ||
RUSTDESK_API_RUSTDESK_WS_HOST: "wss://<font color = blue>monserveur.org</font>/ws" | RUSTDESK_API_RUSTDESK_WS_HOST: "wss://<font color = blue>monserveur.org</font>/ws/" | ||
# Si tu mets l'UI en HTTPS, il faudra passer en WSS : | # Si tu mets l'UI en HTTPS, il faudra passer en WSS : | ||
# RUSTDESK_API_RUSTDESK_API_SERVER: "<nowiki>https</nowiki>://PUBLIC_HOST" | # RUSTDESK_API_RUSTDESK_API_SERVER: "<nowiki>https</nowiki>://PUBLIC_HOST" | ||
| Ligne 120 : | Ligne 120 : | ||
volumes: | volumes: | ||
- ./data:/app/data | - ./data:/app/data | ||
On lance le conteneur : | |||
# docker compose up -d | # docker compose up -d | ||
On récupère le mot de passe Admin dans les logs pour la première connexion web : | |||
# docker logs rustdesk-api | # docker logs rustdesk-api | ||
[INFO] Admin Password Is: <font color = green>MotDePasseAleatoire</font> | [INFO] Admin Password Is: <font color = green>MotDePasseAleatoire</font> | ||
== vhost nginx == | |||
{{Méta bandeau | |||
| niveau = information | |||
| icône = loupe | |||
| texte = Voir [[Nginx_ReverseProxy_LXC_Alpine_Linux|Reverse Proxy Nginx]] | |||
}} | |||
server { | |||
listen 80; | |||
listen [::]:80; | |||
server_name <font color = blue>monserveur.org</font>; | |||
# return 404; | |||
return 301 <nowiki>https://</nowiki>$host$request_uri; | |||
} | |||
server { | |||
server_name <font color = blue>monserveur.org</font>; | |||
error_page 403 https://<font color = blue>monserveur.org</font>; | |||
location / { | |||
#proxy_set_header Upgrade $http_upgrade; | |||
#proxy_set_header Connection "upgrade"; | |||
proxy_set_header Host $host; | |||
proxy_set_header X-Real-IP $remote_addr; | |||
proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for; | |||
proxy_set_header X-Forwarded-Proto $scheme; | |||
proxy_set_header X-Forwarded-Host $host; | |||
proxy_set_header X-Forwarded-Port $server_port; | |||
proxy_pass http://<font color = blue>IP_SERVEUR</font>:21114; | |||
# proxy_pass <nowiki>https:</nowiki>//IP_SERVEUR_WEB:PORT; #Alternatif pour redirection sur https | |||
proxy_buffering off; #activer pour désactiver le "buffering" | |||
} | |||
location = /ws { return 301 /ws/; } | |||
location /ws/ { | |||
proxy_pass http://<font color = blue>IP_SERVEUR</font>:21118/; | |||
proxy_http_version 1.1; | |||
proxy_set_header Upgrade $http_upgrade; | |||
proxy_set_header Connection "upgrade"; | |||
proxy_set_header Host $host; | |||
proxy_read_timeout 3600; | |||
proxy_send_timeout 3600; | |||
} | |||
listen [::]:443 ssl; # managed by Certbot | |||
listen 443 ssl; # managed by Certbot | |||
ssl_certificate /etc/letsencrypt/live/<font color = blue>monserveur.org</font>/fullchain.pem; | |||
ssl_certificate_key /etc/letsencrypt/live/<font color = blue>monserveur.org</font>/privkey.pem; | |||
include /etc/letsencrypt/options-ssl-nginx.conf; | |||
ssl_dhparam /etc/letsencrypt/ssl-dhparams.pem; | |||
add_header Strict-Transport-Security "max-age=31536000" always; | |||
ssl_trusted_certificate /etc/letsencrypt/live/<font color = blue>monserveur.org</font>/chain.pem; | |||
ssl_stapling on; | |||
ssl_stapling_verify on; | |||
server_tokens off; | |||
add_header X-Frame-Options "SAMEORIGIN"; | |||
add_header X-XSS-Protection "1; mode=block"; | |||
add_header X-Content-Type-Options "nosniff"; | |||
} | |||
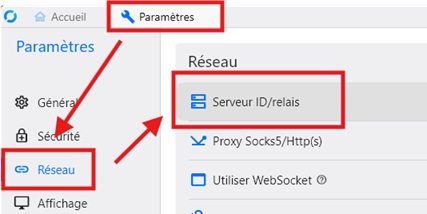
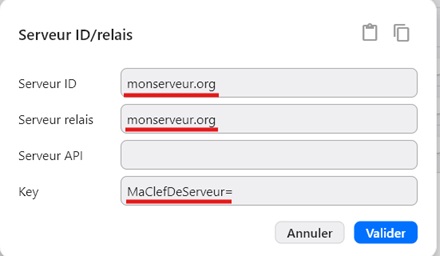
== configuration client == | |||
{{Méta bandeau | |||
| niveau = grave | |||
| icône = important | |||
| texte = La configuration doit être strictement identique sur toutes les machines pour pouvoir se connecter (IP ou DNS). | |||
}} | |||
[[File:Rustsrv3.jpg|border|On renseigne les champs nécessaires..]] | |||
Dernière version du 5 mars 2026 à 18:05
Configuration recommandée pour un LXC Alpine Linux
Type Unprivileged Nesting No CPU 1 vCPU (2 vCPU si nombreux utilisateurs) RAM 128–256 MB (512 MB pour 10 connexions simultanées etc..) Disk 2 GB
Ports à rediriger
21115-21117 TCP 21116 UDP
Installation
apk update apk upgrade apk add --no-cache curl unzip
Créer utilisateur service + dossiers propres :
adduser -D -h /var/lib/rustdesk rustdesk mkdir -p /opt/rustdesk mkdir -p /var/lib/rustdesk chown -R rustdesk:rustdesk /var/lib/rustdesk chmod 700 /var/lib/rustdesk
Télécharger RustDesk Server:
cd /opt/rustdesk curl -fL -o rustdesk.zip https://github.com/rustdesk/rustdesk-server/releases/latest/download/rustdesk-server-linux-amd64.zip unzip -o rustdesk.zip mv amd64/* . rmdir amd64 chown -R rustdesk:rustdesk /opt/rustdesk
Créer les services OpenRC :
cat > /etc/init.d/rustdesk-hbbs <<'EOF'
#!/sbin/openrc-run
name="rustdesk-hbbs"
command="/opt/rustdesk/hbbs"
command_user="rustdesk:rustdesk"
command_background="yes"
pidfile="/run/${RC_SVCNAME}.pid"
directory="/var/lib/rustdesk"
depend() { need net; }
EOF
chmod +x /etc/init.d/rustdesk-hbbs
cat > /etc/init.d/rustdesk-hbbr <<'EOF'
#!/sbin/openrc-run
name="rustdesk-hbbr"
command="/opt/rustdesk/hbbr"
command_user="rustdesk:rustdesk"
command_background="yes"
pidfile="/run/${RC_SVCNAME}.pid"
directory="/var/lib/rustdesk"
depend() { need net; after rustdesk-hbbs; }
EOF
chmod +x /etc/init.d/rustdesk-hbbr
Activer au boot + démarrer :
rc-update add rustdesk-hbbs default rc-update add rustdesk-hbbr default rc-service rustdesk-hbbs start rc-service rustdesk-hbbr start
Récupérer la clé publique
cat /var/lib/rustdesk/id_ed25519.pub
configuration client
lejianwen/rustdesk-api
Interface web de contrôle pour lister les machines connectées et lancer rapidement la connexion via le bouton "LINK".
Prérequis
- Activer "Nesting" et "Keyctl" dans les options du LXC.
- Un Reverse Proxy pour sécuriser les requêtes API et l'accès au panneau de contrôle web.
Installation
# apk add docker docker-cli-compose # rc-update add docker default # rc-service docker start # mkdir -p /opt/rustdesk-api # cd /opt/rustdesk-api
Fichier de configuration du conteneur :
# vi docker-compose.yml
version: "3.8"
services:
rustdesk-api:
image: lejianwen/rustdesk-api:latest
container_name: rustdesk-api
restart: unless-stopped
ports:
- "21114:21114" # Web UI / API
environment:
TZ: "Europe/Madrid"
# Connexion du rustdesk-api .. ton hbbs (interne LAN)
RUSTDESK_SERVER: "192.168.123.456:21115"
RUSTDESK_KEY: "MaClefDeServeur="
# Ce que l'UI/web-client doit ANNONCER aux navigateurs/client
RUSTDESK_API_RUSTDESK_ID_SERVER: "monserveur.org:21115"
RUSTDESK_API_RUSTDESK_RELAY_SERVER: "monserveur.org:2111"
RUSTDESK_API_RUSTDESK_API_SERVER: "https://monserveur.org"
RUSTDESK_API_RUSTDESK_WS_HOST: "wss://monserveur.org/ws/"
# Si tu mets l'UI en HTTPS, il faudra passer en WSS :
# RUSTDESK_API_RUSTDESK_API_SERVER: "https://PUBLIC_HOST"
# RUSTDESK_API_RUSTDESK_WS_HOST: "wss://PUBLIC_HOST"
volumes:
- ./data:/app/data
On lance le conteneur :
# docker compose up -d
On récupère le mot de passe Admin dans les logs pour la première connexion web :
# docker logs rustdesk-api
[INFO] Admin Password Is: MotDePasseAleatoire
vhost nginx
server {
listen 80;
listen [::]:80;
server_name monserveur.org;
# return 404;
return 301 https://$host$request_uri;
}
server {
server_name monserveur.org;
error_page 403 https://monserveur.org;
location / {
#proxy_set_header Upgrade $http_upgrade;
#proxy_set_header Connection "upgrade";
proxy_set_header Host $host;
proxy_set_header X-Real-IP $remote_addr;
proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for;
proxy_set_header X-Forwarded-Proto $scheme;
proxy_set_header X-Forwarded-Host $host;
proxy_set_header X-Forwarded-Port $server_port;
proxy_pass http://IP_SERVEUR:21114;
# proxy_pass https://IP_SERVEUR_WEB:PORT; #Alternatif pour redirection sur https
proxy_buffering off; #activer pour désactiver le "buffering"
}
location = /ws { return 301 /ws/; }
location /ws/ {
proxy_pass http://IP_SERVEUR:21118/;
proxy_http_version 1.1;
proxy_set_header Upgrade $http_upgrade;
proxy_set_header Connection "upgrade";
proxy_set_header Host $host;
proxy_read_timeout 3600;
proxy_send_timeout 3600;
}
listen [::]:443 ssl; # managed by Certbot
listen 443 ssl; # managed by Certbot
ssl_certificate /etc/letsencrypt/live/monserveur.org/fullchain.pem;
ssl_certificate_key /etc/letsencrypt/live/monserveur.org/privkey.pem;
include /etc/letsencrypt/options-ssl-nginx.conf;
ssl_dhparam /etc/letsencrypt/ssl-dhparams.pem;
add_header Strict-Transport-Security "max-age=31536000" always;
ssl_trusted_certificate /etc/letsencrypt/live/monserveur.org/chain.pem;
ssl_stapling on;
ssl_stapling_verify on;
server_tokens off;
add_header X-Frame-Options "SAMEORIGIN";
add_header X-XSS-Protection "1; mode=block";
add_header X-Content-Type-Options "nosniff";
}